After they had usage of Risk-free Wallet ??s method, they manipulated the person interface (UI) that customers like copyright workforce would see. They replaced a benign JavaScript code with code created to alter the intended place from the ETH from the wallet to wallets controlled by North Korean operatives. This destructive code would only conc
 Edward Furlong Then & Now!
Edward Furlong Then & Now!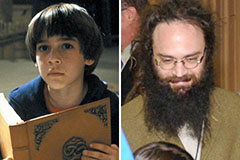 Barret Oliver Then & Now!
Barret Oliver Then & Now! Richard "Little Hercules" Sandrak Then & Now!
Richard "Little Hercules" Sandrak Then & Now! Mike Vitar Then & Now!
Mike Vitar Then & Now! Dawn Wells Then & Now!
Dawn Wells Then & Now!